Generic Bootstrapping Architecture (GBA) is a technology that enables the authentication of a user. This authentication is possible if the user owns a valid identity on an HLR (Home Location Register) or on an HSS (Home Subscriber Server).
GBA is standardized at the 3GPP (http://www.3gpp.org/ftp/Specs/html-info/33220.htm). The user authentication is instantiated by a shared secret, one in the smartcard, for example a SIM card inside the mobile phone and the other is on the HLR/HSS.
GBA authenticates by making a network component challenge the smartcard and verify that the answer is the one predicted by the HLR/HSS.
Instead of asking the service provider to trust the BSF and relying on it for every authentication request, the BSF establishes a shared secret between the simcard card and the service provider. This shared secret is limited in time and for a specific domain.
Strong points
editThis solution has some strong points of certificate and shared secrets without having some of their weaknesses:
- There is no need for user enrollment phase nor secure deployment of keys, making this solution a very low cost one when compared to PKI.
- Another advantage is the ease with which the authentication method may be integrated into terminals and service providers, as it is based on HTTP's well known "Digest access authentication". Every Web server already implement HTTP digest authentication and the effort to implement GBA on top of digest authentication is minimal. For example, it could be implemented on SimpleSAMLPhP http://rnd.feide.no/simplesamlphp Archived 2008-12-19 at the Wayback Machine with 500 PHP lines of code and only a few tens of lines of code are Service Provider specific making it really easy to port it to another Web site.
- On device side is needed:
- A Web browser (in fact an HTTP client) implementing digest authentication and the special case designed by a "3gpp" string in the HTTP header.
- A means to dialog with a smartcard and signed the challenge sent by the BSF, either Bluetooth SAP or a Java or native application could be used to serve the request coming from the browser.
Technical overview
editActually, contents in this section are from external literature.[1]
There are two ways to use GAA (Generic Authentication Architecture).
- The first, GBA, is based on a shared secret between the client and server
- The second, SSC, is based on public-private key pairs and digital certificates.
In the shared secret cases, the customer and the operator are first mutually authenticated through 3G and Authentication Key (AKA) and they agree on session keys which can then be used between the client and services that the customer wants to use. This is called bootstrapping. After that, the services can retrieve the session keys from the operator, and they can be used in some application specific protocol between the client and services.
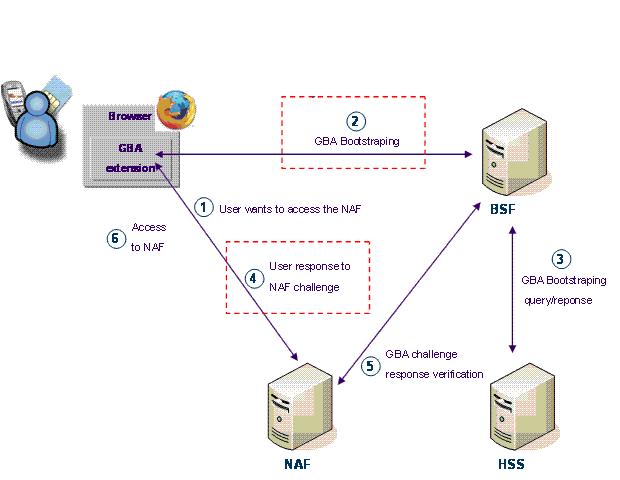
Figure above shows the network GAA entities and interfaces between them. Optional entities are drawn with lines network and borders dotted the scoreboard. The User Equipment (UE) is, for example, the user's mobile phone. The UE and Bootstrapping Server Function (BSF) mutually authenticate themselves during the Ub (number [2] above) interface, using the Digest access authentication AKA protocol. The UE also communicates with the Network Application Functions (NAF), which are the implementation servers, over the Ua [4] interface, which can use any specific application protocol necessary.
BSF retrieves data from the subscriber from the Home Subscriber Server (HSS) during the Zh [3] interface, which uses the Diameter Base Protocol. If there are several HSS in the network, BSF must first know which one to use. This can be done by either setting up a pre-defined HSS to BSF, or by querying the Subscriber Locator Function (SLF). NAFs recover the key session of BSF during the Zn [5] interface, which also uses the diameter at the base Protocol. If NAF is not in the home network, it must use a Zn-proxy to contact BSF .
Uses
edit- The SPICE project developed an extended Use Case named "split terminal" where a user on a PC can authenticate with their mobile phone: http://www.ist-spice.org/demos/demo3.htm Archived 2009-03-24 at the Wayback Machine. The NAF was developed on SimpleSAMLPhP and a Firefox extension was developed to process the GBA digest authencation request from the BSF. Bluetooth SIM Access Profile was used between the Firefox browser and the mobile phone. Later a partner developed a "zero installation" concept.
- The research institute Fraunhofer FOKUS developed an OpenID extension for Firefox which uses GBA authentication.Presentation at ICIN 2008 by Peter Weik
- The Open Mobile Terminal Platform http://www.omtp.org references GBA in its Advanced Trusted Environment: OMTP TR1[2] recommendation, first released in May 2008.
Sadly, despite many advantages and potential uses of GBA, its implementation in handsets has been limited since GBA standardization in 2006. Most notably, GBA was implemented in Symbian-based handsets.
References
edit- ^ "Generic Authentication Architecture by Timo Olkkonen, Helsinki University of Technology" (PDF). Archived from the original (PDF) on 2016-07-05. Retrieved 2010-07-05.
- ^ "OMTP Advanced Trusted Environment: OMTP TR1". Archived from the original on 2008-10-21. Retrieved 2009-01-04.